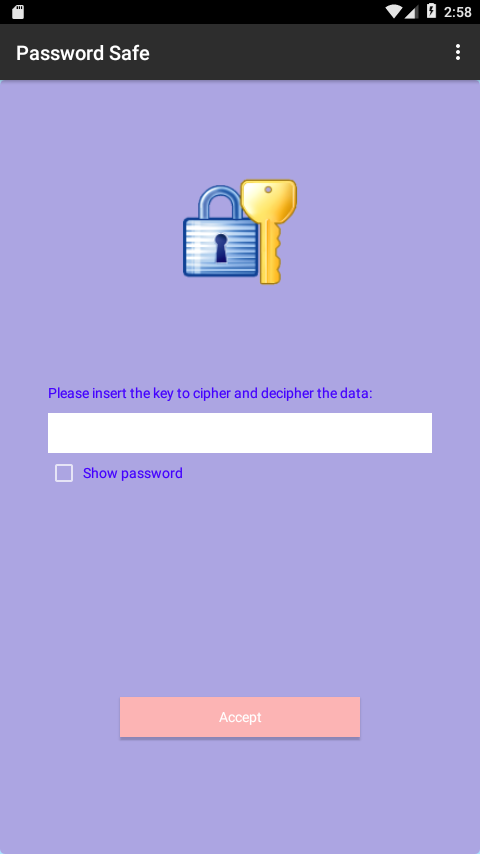
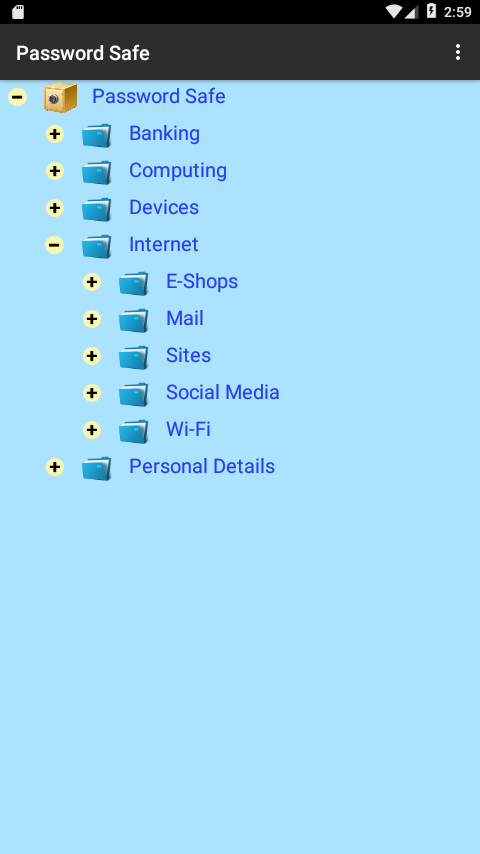
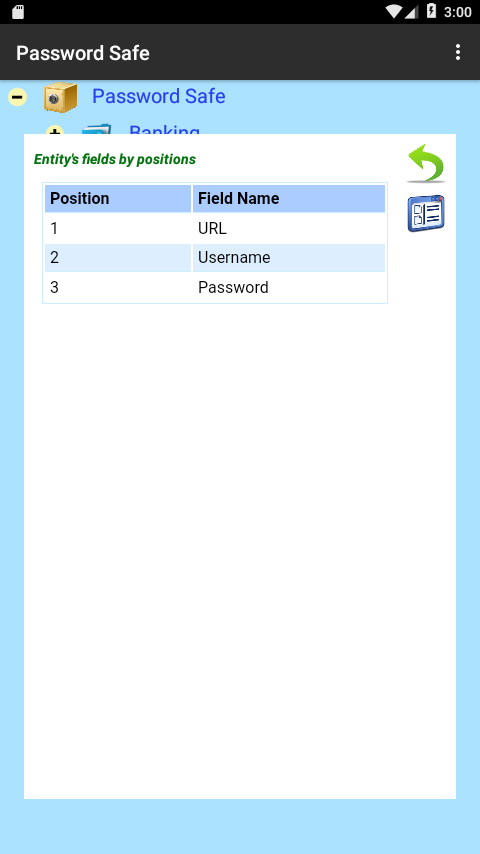
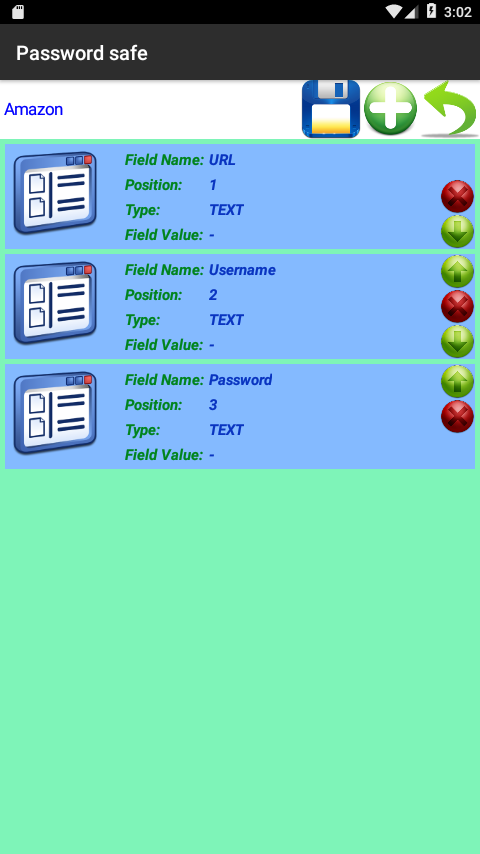
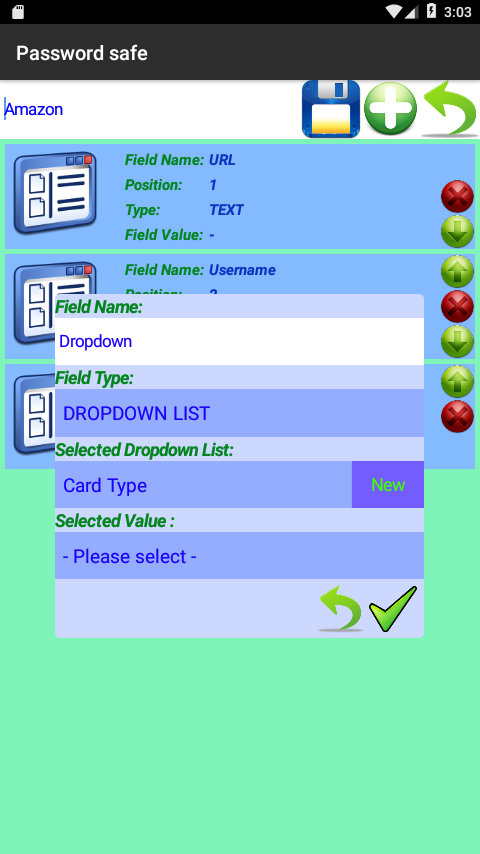
DHQI Password Safe is an application you can use to keep all your sensitive information safe and accessible only by you as it uses a password to allow you to access the information saved. It uses AES256 encryption which means that up until today (2018) no one was able to hack into a program that utilized this kind of Encryption.
Quoting from Wikipedia on AES (Advanced Encryption Standard)
AES has been adopted by the U.S. government and is now used worldwide. It supersedes the Data Encryption Standard (DES), [10] which was published in 1977. The algorithm described by AES is a symmetric-key algorithm, meaning the same key is used for both encrypting and decrypting the data.
In the United States, AES was announced by the NIST as U.S. FIPS PUB 197 (FIPS 197) on November 26, 2001. [7] This announcement followed a five-year standardization process in which fifteen competing designs were presented and evaluated, before the Rijndael cipher was selected as the most suitable (see Advanced Encryption Standard process for more details).
AES became effective as a federal government standard on May 26, 2002, after approval by the Secretary of Commerce. AES is included in the ISO/IEC 18033-3 standard. AES is available in many different encryption packages, and is the first (and only) publicly accessible cipher approved by the National Security Agency (NSA) for top secret information when used in an NSA approved cryptographic module (see Security of AES, below).
Until May 2009, the only successful published attacks against the full AES were side-channel attacks on some specific implementations. The National Security Agency (NSA) reviewed all the AES finalists, including Rijndael, and stated that all of them were secure enough for U.S. Government non-classified data. In June 2003, the U.S. Government announced that AES could be used to protect classified information :
"The design and strength of all key lengths of the AES algorithm (i.e., 128, 192 and 256) are sufficient to protect classified information up to the SECRET level. TOP SECRET information will require use of either the 192 or 256 key lengths. The implementation of AES in products intended to protect national security systems and/or information must be reviewed and certified by NSA prior to their acquisition and use." [15]
AES Security
AES has 10 rounds for 128-bit keys, 12 rounds for 192-bit keys, and 14 rounds for 256-bit keys.
By 2006, the best known attacks were on 7 rounds for 128-bit keys, 8 rounds for 192-bit keys, and 9 rounds for 256-bit keys.[16]
The first key-recovery attacks on full AES were due to Andrey Bogdanov, Dmitry Khovratovich, and Christian Rechberger, and were published in 2011. [28] The attack is a biclique attack and is faster than brute force by a factor of about four. It requires 2 126.2 operations to recover an AES-128 key. For AES-192 and AES-256, 2 190.2 and 2 254.6 operations are needed, respectively. This result has been further improved to 2 126.0 for AES-128, 2 189.9 for AES-192 and 2 254.3 for AES-256, [29] which are the current best results in key recovery attack against AES.
End of wikipedia quoting
To clarify it more if a system was trying to perform key-recovery attacks and was able to perform 10.000.000 trial deciphers in every second of data ciphered with AES256 trying different keys it would take 1.1301114898374702110627762699014•10 62 years to recover the key. In order to understand this better 1000 years are 10 3 years and thus 10 62 years are 1 followed by 62 0 (zeros) years. In order to have a comparable measure the age of the universe is 13.8•10 9 years. It would take 8.1892136944744218192954802166765•10 51 times the age of the universe to recover an AES256 key.
That, translated to plain English, means “ keep your ciphering/deciphering key in your mind or saved in a secured place accessible only by you because if you forget/lose it we will not be able to help you recover your key and thus your data ”.
Full article of Wikipedia on Advanced Encryption Standard
 |
 |
 |
 |
 |